I Today I have seen some news related with the License Agreement of Microsoft on Windows 10…
For what I have read it seems that they will allow themselves to scan all your machine and personal data so they can know you better. 🙂
I believe in good faith but I do not thrust companies that gather more than what is required about us.
I accept the fact that when I am shopping I have to give my name and CC number I do not accept the fact that I have to give my age, gender, GPS coordinates, birth date and all other information that are not required to complete the service.
I found the statements strange about this data privacy policies, with curiosity I have started to read some policy documents and collect more information about this.
This is what I have found in the Windows 10 License Agreement.
“Privacy; Consent to Use of Data. Your privacy is important to us. Some of the software features send or receive information when using those features. Many of these features can be switched off in the user interface, or you can choose not to use them. By accepting this agreement and using the software you agree that Microsoft may collect, use, and disclose the information as described in the Microsoft Privacy Statement (aka.ms/privacy), and as may be described in the user interface associated with the software features.”
This is a very brief statement that points to other page and policy…
What does this means?!!?
I have checked the other page that they call aka.ms/privacy and found this user terms :
Personal Data we Collect Microsoft collects data to operate effectively and provide you the best experiences with our services. You provide some of this data directly, such as when you create a Microsoft account, submit a search query to Bing, speak a voice command to Cortana, upload a document to OneDrive, or contact us for support. We get some of it by recording how you interact with our services by, for example, using technologies like cookies, and receiving error reports or usage data from software running on your device. We also obtain data from third parties (including other companies). For example, we supplement the data we collect by purchasing demographic data from other companies. We also use services from other companies to help us determine a location based on your IP address in order to customize certain services to your location. The data we collect depends on the services and features you use, and includes the following.
Name and contact data. We collect your first and last name, email address, postal address, phone number, and other similar contact data.
Credentials. We collect passwords, password hints, and similar security information used for authentication and account access.
Demographic data. We collect data about you such as your age, gender, country and preferred language.
Interests and favorites. We collect data about your interests and favorites, such as the teams you follow in a sports app, the stocks you track in a finance app, or the favorite cities you add to a weather app. In addition to those you explicitly provide, your interests and favorites may also be inferred or derived from other data we collect.
Payment data. We collect data necessary to process your payment if you make purchases, such as your payment instrument number (such as a credit card number), and the security code associated with your payment instrument.
Usage data. We collect data about how you interact with our services. This includes data, such as the features you use, the items you purchase, the web pages you visit, and the search terms you enter. This also includes data about your device, including IP address, device identifiers, regional and language settings, and data about the network, operating system, browser or other software you use to connect to the services. And it also includes data about the performance of the services and any problems you experience with them.
Contacts and relationships. We collect data about your contacts and relationships if you use a Microsoft service to manage contacts, or to communicate or interact with other people or organizations.
Location data. We collect data about your location, which can be either precise or imprecise. Precise location data can be Global Position System (GPS) data, as well as data identifying nearby cell towers and Wi-Fi hotspots, we collect when you enable location-based services or features. Imprecise location data includes, for example, a location derived from your IP address or data that indicates where you are located with less precision, such as at a city or postal code level.
Content. We collect content of your files and communications when necessary to provide you with the services you use. This includes: the content of your documents, photos, music or video you upload to a Microsoft service such as OneDrive. It also includes the content of your communications sent or received using Microsoft services, such as the: subject line and body of an email, text or other content of an instant message, audio and video recording of a video message, and audio recording and transcript of a voice message you receive or a text message you dictate. Additionally, when you contact us, such as for customer support, phone conversations or chat sessions with our representatives may be monitored and recorded. If you enter our retail stores, your image may be captured by our security cameras. You have choices about the data we collect. When you are asked to provide personal data, you may decline. But if you choose not to provide data that is necessary to provide a service, you may not be able to use some features or services. Service-specific sections below describe additional data collection practices applicable to use of those services.
All this seems global to several services that Microsoft supplies to their customers.
The email situation is particularly strange…
Microsoft sells Office 365 services to companies, does this policy means that all their emails and documents contents are read and stored somewhere in a Microsoft Database? This gives Microsoft a huge power on the markets or Competitive Intelligence if they use this data.
Should we in good faith trust a corporation this information?
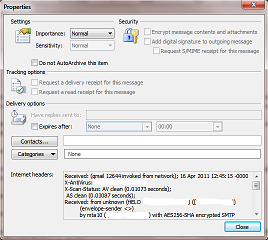
Google refuses to receive or relay encrypted email, I am now curious to see if the same happens in Outlook.com 🙂
This is global policy and might or might not apply to windows 10.
Thinking again the integration of Windows 10 with the other services will cause that windows 10 indirectly will make use of this license agreements… By using their extra services we might get covered by this policies without conscience and somewhere in time we will be giving Microsoft more information than what we wished…
Now in my thoughts Windows 10 free upgrade seems more interesting as it seems to be used as a strategy to sooner or later people use other Microsoft cloud services and then most of this policies will apply and in the end Microsoft will have more power over people and lots of valuable aggregated data. If you use some of the advertised functionalities of Windows 10 you will have to use the cloud services, if you fall on that sweet talk you will be giving money and bonus value (information) to Microsoft.
Unless this companies explain very well:
1 – How the info is protected from third parties.
2 – How the info is protected from employees of the company
3 – How that info is processed
I will get suspicious.
Probably even after reading this information I will continue to be suspicious on this companies…
I did not manage to find all this until the moment.
It would be more easy to have in this huge amount of policies something like how we protect your data…
I am not a lawyer but Microsoft is an American company so if NSA requests information from this databank I don’t think Microsoft can refuse…
Because this seems to be a global Policy lets see what specific information Microsoft collects from Windows 10 Operating systems, not counting with other services integration…
Location Services Windows location service. Microsoft operates a location service that helps determine the precise geographic location of a specific Windows device. Depending on the capabilities of the device, location is determined using satellite global positioning service (GPS), detecting nearby cell towers and/or Wi-Fi access points and comparing that information against a database that Microsoft maintains of cell towers and Wi-Fi access points whose location is known, or deriving location from your IP address. When the location service is active on a Windows device, data about cell towers and Wi-Fi access points and their locations is collected by Microsoft and added to the location database after removing any data identifying the person or device from which it was collected. Microsoft may also share de-identified location data with third parties to provide and improve location and mapping services. Windows services and features (such as browsers and Cortana), applications running on Windows, and websites opened in Windows browsers can access the Windows location service to determine location if you allow them to do so. Some features and apps request location permission when you first install Windows, some ask the first time you use the app, and others ask every time you access the location service. For information about certain Windows apps that use the location service, see the Windows Apps section below. Data about a Windows device’s recent location history is stored on the device, and certain apps and Windows features can access this location history. You can clear your device’s location history at any time in the device’s Settings menu. In Settings, you can also view which applications have access to the location service or your device’s location history, turn off or on access to the location service for particular applications, or turn off the location service. Note that on mobile devices, your mobile operator will have access to your location even if you turn off the location service. Find My Phone. The Find My Phone feature allows you to find the location of your Windows phone from https://account.microsoft.com, even if you have turned off all access to the location service on the phone. If you have turned on the “save my location every few hours” feature in the Find My Phone settings on your phone, the Find My Phone feature will periodically send and store a single last known location of your phone, even if you have turned off location services on your phone. Each time a new location is sent, it replaces the previously-stored location. Find My Device. The Find My Device feature allows an administrator of a Windows PC or tablet to find the location of that device if the administrator has enabled the location service for the device, even if other users have disabled location for themselves. When the administrator attempts to locate the device, users will see a notification in the notification center. Windows Motion Sensing. Windows devices with motion activity detection can collect motion activity. This data can enable features such as a pedometer to count the number of steps you take, so a fitness application can estimate how many calories you burn. This data and history is stored on your device and can be accessed by applications you give permission to access and use that data.
Most of the personal things on the computer can be disabled so theoretically you can control what you give.
That is good and correct from manufacturer but what happens when you start using all other cloud services?
For some information it really does not need to collect data from your computer or GPS, all it needs is to correlate data using your IP with third-party information and it will know where you are, it will be even better if it gets your BSSID or SSID.
Reading a bit more…
Your backup of encryption key goes to the OneDrive where probably enters in the Backup cycle of Microsoft Cloud and can be stored for some time… even after we delete it… 🙂
Device encryption. Device encryption helps protect the data stored on your device by encrypting it using BitLocker Drive Encryption technology. When device encryption is on, Windows automatically encrypts the drive Windows is installed on and generates a recovery key. The BitLocker recovery key for your device is automatically backed up online in your Microsoft OneDrive account.
Information of our connectivity is also interesting…
Remember when I said they only need to get your IP or BSSID or SSID?
Here is the policy on what they collect from us.
Usage and connectivity data. Microsoft regularly collects basic information about your Windows device including usage data, app compatibility data, and network and connectivity information. This data is transmitted to Microsoft and stored with one or more unique identifiers that can help us recognize an individual user on an individual device and understand the device’s service issues and use patterns. The data we collect includes: Configuration data, including the manufacturer of your device, model, number of processors, display size and resolution, date, region and language settings, and other data about the capabilities of the device. The software (including drivers and firmware supplied by device manufacturers), installed on the device. Performance and reliability data, such as how quickly programs respond to input, how many problems you experience with an app or device, or how quickly information is sent or received over a network connection. App use data for apps that run on Windows (including Microsoft and third party apps), such as how frequently and for how long you use apps, which app features you use most often, how often you use Windows Help and Support, which services you use to sign into apps, and how many folders you typically create on your desktop. Network and connection data, such as the device’s IP address, number of network connections in use, and data about the networks you connect to, such as mobile networks, Bluetooth, and identifiers (BSSID and SSID), connection requirements and speed of Wi-Fi networks you connect to. Other hardware devices connected to the device. Some diagnostic data is vital to the operation of Windows and cannot be turned off if you use Windows. Other data collection is optional, and you will be able to turn this data collection on or off in Settings.
Why they need my BSSID and SSID???
If I am using a public one, for what I have read, they buy that info from third parties, if it is personal why do they need to have it?
And finally I love the last statement “Some diagnostic data is vital to the operation of Windows and cannot be turned off if you use Windows.“
I am now curious if some companies when they give this diagnostics to Microsoft really know what is in the package…
I believe some know but most just have good faith. Same as users.
What is this part that we can’t disable and keeps feeding Microsoft with our data?!?!?!
In reality this makes redundant the GPS situation… the difference is just the precision that they can pin point you on the map.
Also this is interesting, if you use a wi-fi network and you use Tor to make your traffic anonymous it means that somehow in specific situations they can get your wi-fi information? That information correlated with other info will make Tor useless…
This with the policy that you are forced to accept windows updates makes me think in some more conspiracy theories… 😛
Probably is some requirement that governments need…
Speaking of data retention…
Microsoft retains personal data for as long as necessary to provide the services and fulfill the transactions you have requested, or for other essential purposes such as complying with our legal obligations, resolving disputes, and enforcing our agreements. For example: For Bing search queries, we de-identify stored queries by removing the entirety of the IP address after 6 months, and cookie IDs and other cross-session identifiers after 18 months. In Outlook.com, when your Deleted Items folder is emptied, those emptied items remain in our system for up to 30 days before final deletion. If you remove a credit card from your account, Microsoft will retain transaction records containing your credit card number for as long as reasonably necessary to complete any existing transactions, to comply with Microsoft’s legal and reporting requirements, and for the detection and prevention of fraud.
Strangely I did not find nothing related with OneDrive Retention Policy… Remember the place where it is stored our encryption key?!!!
Well I found all this in around 2 hours reading policies and jumping around from one to another…
I might be wrong but it seems in some cases they are collecting more that what they need to provide us the services they sell.
I hope this creates more awareness to people and they can decide in conscience if they want to give or not personal information control to corporations.